Key Insights
Makina Finance, a decentralized finance (DeFi) protocol, has reportedly suffered a major security breach resulting in losses estimated at approximately $5 million.
The exploit targeted a specific liquidity pool and was executed using a flash loan–based oracle manipulation strategy.
Although the attacker initiated the exploit, a Maximal Extractable Value (MEV) bot front-ran the transaction, capturing roughly $4.1 million of the total drained funds.
Makina Finance has confirmed the exploit, stating that the incident was isolated and did not compromise all protocol pools.
The protocol has activated emergency security measures while continuing its investigation into the attack.
- Key Insights
- Overview of the Makina Finance Exploit
- Timeline of the Attack
- Understanding the Vulnerable Pool: DUSD/USDC Stableswap
- How the Exploit Worked: Step-by-Step Breakdown
- The Role of the MEV Bot
- Where Did the Funds Go?
- Conflicting Estimates of the Losses
- Makina Finance Responds
- Impact on Liquidity Providers and Users
- Broader Implications for DeFi Security
- A Pattern of DeFi Exploits in 2026
- Lessons for Developers and Investors
- FAQ’s
- What happened to Makina Finance?
- Which pool was affected by the exploit?
- How did the attacker execute the exploit?
- Why did an MEV bot take most of the stolen funds?
- How much money was ultimately lost in the attack?
- What actions has Makina Finance taken following the exploit?
- What does this incident mean for DeFi users and investors?
- Conclusion
The incident underscores ongoing vulnerabilities within DeFi systems, particularly around oracle design, permissionless functions, and flash loan mechanics.
Overview of the Makina Finance Exploit
Decentralized finance protocol Makina Finance has become the latest victim in a growing list of blockchain platforms affected by sophisticated smart contract exploits. The attack, first flagged by blockchain security firm CertiK, occurred late Monday and resulted in millions of dollars being siphoned from one of Makina’s liquidity pools.
According to initial findings, the exploit was limited to Makina Finance’s Dialectic USD (DUSD) / USDC stableswap pool, a liquidity pool designed to facilitate low-slippage trades between two stable-value assets. While the broader Makina ecosystem was not directly compromised, the targeted pool suffered severe losses, shaking confidence among liquidity providers and raising fresh concerns about DeFi security architecture.
What makes this incident particularly notable is not just the exploit itself, but the role of an MEV bot that intervened mid-attack, effectively outcompeting the original attacker and extracting the majority of the funds.
Timeline of the Attack
Blockchain forensic analysis suggests that the exploit was carried out in a single, highly optimized transaction, a hallmark of modern DeFi attacks. The attacker leveraged a massive flash loan to manipulate price data used by Makina Finance’s internal oracle system.
Shortly after the exploit transaction was broadcast to the network, an MEV bot detected the opportunity and front-ran a portion of the exploit, executing its own set of trades that captured a significant share of the available liquidity.
Within minutes, the affected pool was effectively drained, and the stolen funds were dispersed across multiple blockchain addresses, complicating recovery efforts.
Understanding the Vulnerable Pool: DUSD/USDC Stableswap
At the center of the incident was Makina Finance’s DUSD/USDC stableswap pool. Stableswap pools are designed to facilitate efficient exchanges between assets with similar values, such as stablecoins pegged to the US dollar.
However, the DUSD pool had a distinctive architectural feature that ultimately contributed to its downfall: a function known as updateTotalAum.
This function allowed permissionless updates to the pool’s total assets under management (AUM), a mechanism intended to ensure flexibility and decentralization. Unfortunately, this design choice also introduced a critical attack vector.
How the Exploit Worked: Step-by-Step Breakdown
Flash Loan Acquisition
The attacker initiated the exploit by taking out an enormous $280 million USDC flash loan. Flash loans allow users to borrow large sums of cryptocurrency without collateral, provided the loan is repaid within the same transaction.
While flash loans are a legitimate DeFi innovation, they have increasingly become a tool of choice for attackers due to the immense temporary capital they provide.
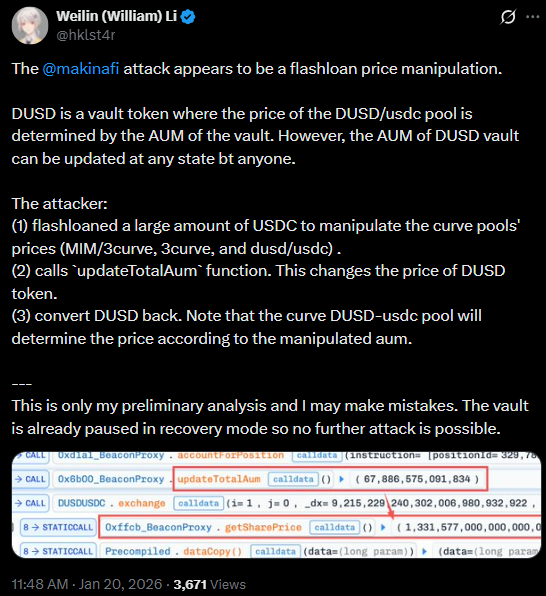
Oracle Manipulation
Out of the $280 million borrowed, approximately $170 million USDC was used to manipulate Makina Finance’s MachineShareOracle, the pricing mechanism responsible for determining the exchange rate between DUSD and USDC in the stableswap pool.
Because the oracle relied on on-chain values that could be influenced within a single transaction, the attacker was able to artificially skew the perceived price of DUSD.
Permissionless AUM Update
The attacker then exploited the permissionless updateTotalAum function, refreshing the oracle’s price mid-transaction. This step was crucial, as it allowed the manipulated price to be recognized as legitimate by the protocol before any safeguards could intervene.
CertiK security engineer, known by the pseudonym “nobody,” highlighted this step as the defining weakness in the attack:
The pool’s design allowed anyone to update the total AUM without restrictions, enabling attackers to freely influence pricing mechanisms during a transaction.
Pool Drainage
With the oracle price distorted, the attacker used the remaining $110 million USDC to execute a series of swaps that drained approximately $5 million USDC from the DUSD/USDC pool.
The entire exploit was completed in a single atomic transaction, leaving little opportunity for automated defenses or manual intervention.
The Role of the MEV Bot
While the attacker initiated the exploit, they were not the primary beneficiary.
An MEV bot, operating from the address 0xa6c2, detected the vulnerable transaction in the mempool and strategically front-ran portions of the exploit. By submitting transactions with higher gas fees, the bot was able to execute its trades before the attacker’s final steps.
As a result, the MEV bot captured approximately $4.1 million, representing the majority of the drained funds.
What Is MEV?
MEV, or Maximal Extractable Value, refers to the profit that can be extracted by reordering, inserting, or censoring transactions within a blockchain block. MEV bots constantly monitor pending transactions, searching for arbitrage opportunities, liquidations, or exploits they can capitalize on.
In this case, the MEV bot effectively acted as a secondary attacker, exploiting the same vulnerability faster than the original hacker.
Where Did the Funds Go?
On-chain analysis shows that the MEV bot transferred the stolen funds to two newly created wallet addresses, a common tactic used to obscure fund movement and complicate tracking.
Meanwhile, it remains unclear how much, if any, of the funds were ultimately retained by the original attacker, given the bot’s intervention.
Conflicting Estimates of the Losses
Different blockchain security firms have reported varying figures regarding the total amount drained:
- CertiK: Approximately $5 million
- PeckShield: Around $4.13 million
- GoPlus: Roughly $5.1 million
- TenArmor: Estimated $4.2 million
These discrepancies are not unusual in DeFi exploits, as asset valuations can fluctuate rapidly and depend on the methodology used to calculate losses.
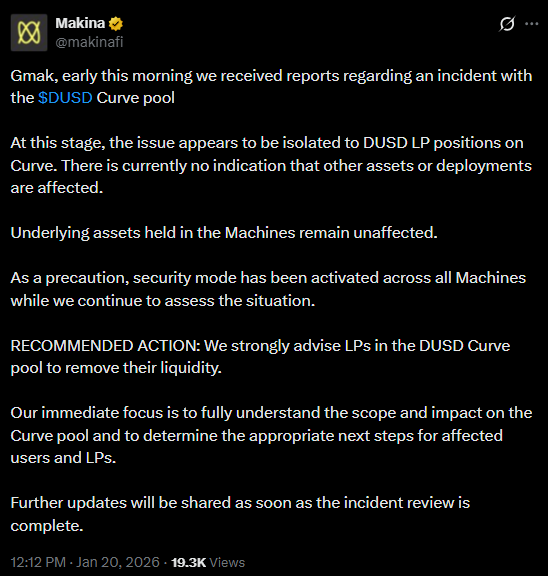
Makina Finance Responds
Makina Finance has officially acknowledged the exploit, confirming that it affected only a single liquidity pool and did not compromise the entire protocol.
In a statement shared with the community, the protocol emphasized that the incident was isolated and that immediate steps had been taken to mitigate further risk.
Emergency Measures Implemented
- Activation of security mode across all Machines
- Recommendation for liquidity providers to withdraw funds from the DUSD Curve pool
- Ongoing internal and third-party security audits
- Temporary restrictions on certain protocol functions
Makina Finance stated that it is continuing to investigate the incident and will communicate next steps for affected users once the analysis is complete.
Impact on Liquidity Providers and Users
For liquidity providers in the affected pool, the exploit represents a direct financial loss. While Makina Finance has not yet announced a compensation plan, such decisions often depend on treasury reserves, insurance coverage, or community governance votes.
The incident may also have broader implications for user trust, particularly among participants who prioritize protocol safety and risk management.
Broader Implications for DeFi Security
The Makina Finance exploit highlights several persistent challenges in the DeFi ecosystem:
Oracle Design Risks
Oracles remain one of the most frequently exploited components in DeFi protocols. Any mechanism that allows price updates within the same transaction as a trade introduces significant risk.
Permissionless Functions
While permissionless design aligns with decentralization principles, unrestricted access to sensitive functions—such as AUM updates—can create critical vulnerabilities if not properly constrained.
Flash Loan Abuse
Flash loans continue to amplify the impact of exploits by enabling attackers to wield massive capital with minimal upfront risk.
MEV as a Double-Edged Sword
MEV bots are often framed as neutral or even beneficial market participants, but incidents like this demonstrate how they can exacerbate losses during exploits.
A Pattern of DeFi Exploits in 2026
The Makina Finance incident is not an isolated case. This year alone, several DeFi platforms have suffered significant losses:
- Trubit fell victim to exploited smart contract vulnerabilities
- YO Protocol experienced losses attributed to human error
- Multiple smaller platforms reported oracle manipulation and flash loan attacks
Despite improvements in auditing tools and security practices, DeFi remains a high-risk environment, particularly for protocols managing large pools of on-chain liquidity.
Lessons for Developers and Investors
For developers, the exploit reinforces the importance of:
- Rigorous security audits
- Restricting permissionless access to sensitive functions
- Implementing time-weighted or multi-source oracle pricing
- Stress-testing protocols against flash loan scenarios
For investors and liquidity providers, it serves as a reminder to:
- Diversify across platforms
- Monitor protocol updates and audits
- Understand the technical risks of yield-generating strategies
Read More: Pi Coin Drops 10% to All-Time Low Ahead of 140M Token Unlock
FAQ’s
What happened to Makina Finance?
Makina Finance suffered a smart contract exploit that drained approximately $5 million from one of its liquidity pools. The attack targeted the DUSD/USDC stableswap pool and involved oracle manipulation using a flash loan.
Which pool was affected by the exploit?
The incident affected Makina Finance’s Dialectic USD (DUSD) / USDC stableswap pool. According to the protocol, other pools and core infrastructure were not compromised.
How did the attacker execute the exploit?
The attacker used a large USDC flash loan to manipulate Makina’s pricing oracle. By exploiting a permissionless function that allowed updates to the pool’s total assets under management, the attacker distorted token prices and drained funds in a single transaction.
Why did an MEV bot take most of the stolen funds?
An MEV bot detected the exploit transaction in the mempool and front-ran the attacker by submitting transactions with higher gas fees. As a result, the bot captured around $4.1 million of the total funds drained from the pool.
How much money was ultimately lost in the attack?
Reported losses vary by blockchain security firm. Estimates range from approximately $4.1 million to $5.1 million, depending on valuation methods and timing of the transactions.
What actions has Makina Finance taken following the exploit?
Makina Finance confirmed the incident, activated security mode across all Machines, and advised liquidity providers to withdraw funds from the affected pool. The team is conducting an investigation and reviewing security measures to prevent similar incidents.
What does this incident mean for DeFi users and investors?
The exploit highlights ongoing risks in DeFi, particularly around oracle design and flash loan exposure. Users and liquidity providers are encouraged to assess protocol security, diversify risk, and stay informed about updates and audits before committing funds.
Conclusion
The Makina Finance exploit is a stark reminder that even well-designed DeFi protocols remain vulnerable to sophisticated attacks. While the incident was limited in scope, the combination of oracle manipulation, permissionless contract functions, and MEV interference resulted in millions of dollars in losses.
As Makina Finance continues its investigation and implements safeguards, the broader DeFi ecosystem must reflect on the lessons learned. Without stronger security standards and more resilient design frameworks, similar exploits are likely to continue reshaping the decentralized financial landscape.